Fraud and Security Information
EVENTS | NEWSLETTERS | FRAUD & SCAMS
Part of managing your finances is to be on the lookout for fraudulent activity on your accounts or in your name. Below is some information that can help you protect your accounts, credit and debit cards, and personal information from criminals. You will also find information about steps to take should you experience account fraud or identity theft.
Please contact us if you have any questions or concerns about any activity on your account or a suspicious letter, email, phone call, or text.
Scam Alert: Regarding Jury Duty - Updated 1/8/2026
Community Credit Union of Florida has been made aware of scammers contacting people by phone or text stating they you have failed to show up for jury duty.
This is a SCAM. You will never be contacted by phone regarding missed jury duty. Official documents are only sent via US mail.
If you receive this type of call, hang up and call us to report the fraudulent attempt to scam you. You may also contact your local clerk of courts to confirm jury duty status.
Beware of a Scam That is Targeting Members
Community Credit Union of Florida is aware of a spoofing scam targeting members. Some members have received calls from a number that appears to come from CCU Florida and fraudsters are posing as credit union employees offering to help with fraudulent transactions. They have asked for identifying information including usernames, passwords, PINs, and authentification codes to gain access to the members account. If you receive a call or text like this, DO NOT GIVE ANY INFORMATION, and either hang up the call or do not reply to the text.
Spoofing is a fraudulent practice where communication such as a phone call, text or email is disguised to look like it is coming from a legitimate company. Fraudsters gain your trust and ask for personal information to get access to accounts using different tactics.
It is important to stay vigilant so you can be the first and best line of defense.
While CCU Florida may contact you if they suspect fraudulent transactions on your account, they will never ask for the following:
- User ID/Username
- Passwords
- Authentication codes sent to you via text or email
- PIN numbers
- CVV codes (the 3-digit number on the back of your debit or credit cards)
If someone calls you and you are unsure whether the call is legitimate, do not provide any personal information to the caller. Ask for their name and tell them you will call them back. Only call our direct number 321.690.2328 (toll-free 800.690.2338). Remember, CCU Florida has 24/7 phone support.
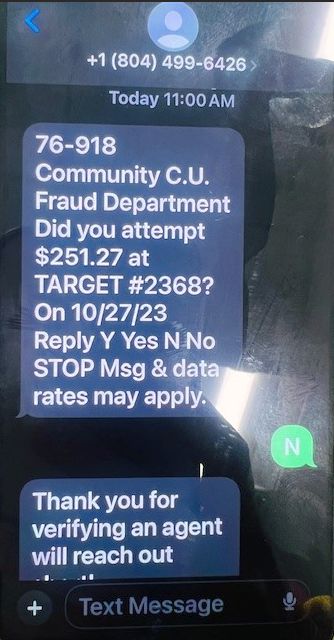
Fraudulent Text Messages
Fraudulent texts have recently been reported encouraging members to verify debit transactions.When a member verifies yes or no, a text will be sent asking the member to call a phone number where they are asked questions about their account, or you will receive a phone call from them. These texts look very similar to the legitimate texts our fraud department may send to members when there is a real issue. Legitimate CCU Florida text's will instruct you to only contact this phone number: 1.855.961.1602. We will update if further information comes in about his activity. See image of text below.
Please know that CCU Florida will never ask you for your PIN, passwords or your full card number. If you receive a text of have concerns, please reach out to us at 321.690.2328 (toll-free 1.800.690.2338), option 5 to report any suspicious texts.
Alert: SIM Swapping and Port-Out Fraud Leads to Account Takeovers
Fraudsters are hijacking members’ mobile devices through SIM (Subscriber Identity Module) swapping and port-out scams that result in account takeovers. Both scams provide the fraudster with the ability to receive calls and SMS text messages intended for the mobile phone users.
- In the SIM swapping scam, a fraudster impersonates a mobile phone user and social engineers the user’s mobile phone carrier into activating a replacement SIM card the fraudster has in their possession.
- The port-out scam is similar except that the fraudster social engineers a mobile phone carrier into porting the user’s mobile phone to a different carrier.
How to help protect yourself:
- Consider putting a port freeze or PIN or password on your mobile carrier account. This will help prevent a SIM swap and/or porting service to another carrier.
- Check with your carrier to see if they have any features that could potentially stop SIM swapping. For example, Verizon has a feature that can be enabled from their My Verizon app called “Number Lock.” This feature enables customers to prevent an unauthorized port out or SIM swap of your mobile number.
If you suspect you have been a victim of one of these scams, please stop in any branch or call our main number 321-690-2328 and speak to a Member Services Representative (option 5) who can help make sure your accounts are safe.
Debit and Credit Card Scam Leads to Fraudulent P2P Transactions
The scammer calls from what appears to be Community Credit Union’s phone number (1-800-690-2338), says there has been suspicious activity on the member’s card, and offers to close the card for the member. In most cases, the scammer already knows part or all of the member’s card number. The scammer then sends a one-time passcode to the member’s phone which the member is instructed to provide for verification. This code is then used by the scammer to register for Apple Pay or Samsung Pay. With this access, the scammer then conducts fraudulent transactions on the member’s card.
If you receive a call from someone claiming to be from CCU and asking for a verification code, please hang up, and contact Member Services right away at 321-690-2328 (option 5) to report the incident.
PLEASE BE AWARE: Community Credit Union of Florida will NEVER contact you asking for your account number, credit card number, Personal Identification Number (PIN), online banking user name/password, one-time verification code, or to confirm a family member's personal information. If someone emails, calls, or texts you asking for this information, it is a scam. DO NOT FOLLOW THE INSTRUCTIONS.
If you receive a suspicious phone call, text, or voice mail message from someone claiming to be from CCU, please call our main number 321-690-2328 and speak to a Member Services Representative (option 5) who can confirm whether or not the call was legitimate.
According to CUNA Mutual some common scams to be aware of include:
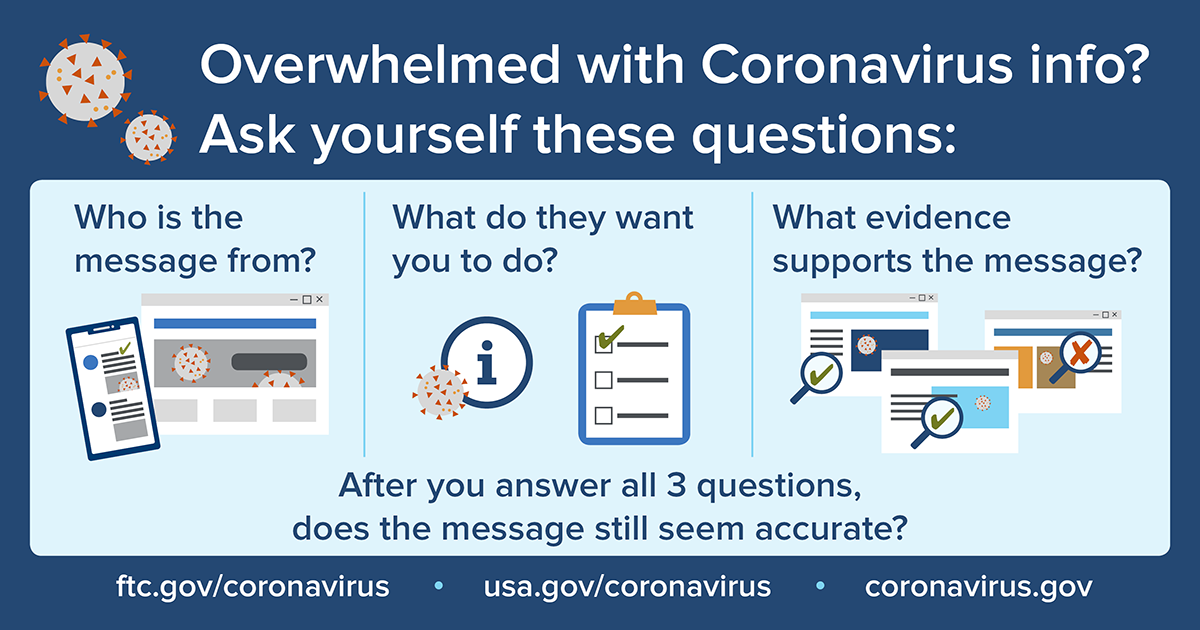
Beware of COVID-19 Scams
Unfortunately, there are always some criminals who try to take advantage of fears and vulnerabilities. The current concerns regarding COVID-19 are no exception.
Abbreviating the year 2020 could leave you open to fraud
The new year is giving scammers an easy way to forge documents, but you can protect yourself by not abbreviating the year.Why? This year’s abbreviation is easily changeable and could be used against you. The concern is that scammers could easily manipulate a document or check dated “1/7/20” into “1/7/2000” or even “1/7/2021.”
In the future, post-dating could also be a problem. For example, a check dated “1/7/20” could become “1/7/2021” next year, possibly making an uncashed check active again. A similar method could be used for debts that are past the statute of limits.
The solution is easy: Be sure to write out the full date. And, spelling out the month out can also help.
ATM/Debit Card Security
Just as you would protect your cash, please take a few steps to protect your cards:
Protect Yourself Online
Learn how to protect yourself and children online at this site from the Federal Trade Commission: OnGuard Online
Spoofing
Spoofing is the act of disguising a communication as being from a known, trusted source. For example, with caller ID spoofing, it can appear as if the phone call is coming from a specific number—either one that is known and/or trusted to the recipient, or one that indicates a specific geographic location. Attackers can then use social engineering—often posing as someone from a credit union—to convince their targets to provide sensitive information such as account numbers.
The primary way to protect against spoofing is to be vigilant and wary of the information the caller is requesting. Even if the number looks legitimate, hang up and call the number yourself, as caller ID numbers can be spoofed.
Spoofing can sometimes be easy to spot, but not always—malicious scammers can carry out sophisticated spoofing attacks that require vigilance on the part of the user. Being aware can help you avoid being a victim.
Fraudulent Phone Calls
We have received reports of phone calls to members claiming to be from Falcon, which is a legitimate fraud protection company, asking to confirm a transaction. However, the caller then states that in order to assist the member, the member would have to provide the online banking user name and password. This is NEVER needed for fraud protection calls. Hang up immediately.
Government Imposter Scams
The FTC’s latest Data Spotlight shows the surge in reports about government imposters. People are reporting calls from – and losing money to – scammers pretending to be the Social Security Administration, IRS, Medicare, a government grants group, cops, or the FBI. Please keep in mind:
Romance Scams
Romance scammers most often use fake online profiles and may use photos from the web to create attractive and convincing phony profiles. They might make up names or assume the identities of real people on dating apps or social media sites. Once scammers have someone by the heartstrings, they say they need money, often for a medical emergency, misfortune, or pretending to need help with travel costs for a long-awaited visit. Some claim to be in the military and stationed abroad, which explains why they can’t meet in person. Reports of romance scams more than doubled and reported losses increased more than fourfold from 2015 to 2018.
So what can singles do to play it safe while dating online? Here are some tips to help spot bogus suitors:
Identity Theft
Identity theft is a serious crime that occurs when someone uses your personal information, such as your name, Social Security number, driver's license, credit card number, or other sensitive and confidential information without your permission to commit fraud or other damaging crimes. Unfortunately, no individual can control whether he/she will become a victim; however, you can minimize your risk by managing your personal information.
Click on the image below to view a Financial Fitness Minute on avoiding identity theft. You can also find additional resources on many aspects of preventing and recovering from identity theft on the BALANCE web site.
Fake Check Scams
If it sounds too good to be true, it probably is…
Unfortunately, some fraud is caused when account holders unwittingly participate in a scam. A popular one is the Fake Check Scam. Here’s an example: Someone is given a $1,000 check to deposit and told to withdraw $800 and send that back to the individual who provided the check, and keep the check is from and keep the $200 as payment for doing this. Scammers use counterfeit checks in many scenarios - connected with a sweepstakes, a job offer to be a "mystery shopper" at some store, or even an offer for putting a decorative wrapper around your car.
Seems like a quick way to make money without having to do much. But, ultimately the check deposited will be determined to be a bad check, and you now owe the entire amount of the check to their financial institution.
Skimming Scams
Skimming happens when an illegal copy of a credit, debit or ATM card is made when the original was being used during a normal transaction process. Typical methods of skimming involve use of a modified card reader that reads and stores all the sensitive information that the original card contains, such as Personal Identification Numbers (PIN). This information is then used to make counterfeit cards. When using an ATM, it is important to be suspicious of anything that seems unusual, such as odd-looking equipment, noticeable wires that are suspiciously attached to the machine, or a jammed machine that forces you to use another ATM where the actual skimming device might be attached. In addition, also be sure to check your account statements regularly to make sure there are no unusual or unauthorized transactions that were debited from it.
Traveling Abroad
Card issuers like CCU have practices in place that are intended to protect you from fraud. Some card companies, in an attempt to prevent fraudulent charges on your account, may put a hold on your card for suspicious activity if they are not aware of your travel plans, or they may even place a freeze on a country if it is discovered that fraudulent card perpetrators are known to be working within that country. It is also a good idea to contact each of your card companies before leaving on your trip to notify them that you're traveling internationally and to check their policies. Please take a few minutes to call a Member Service Representative at 321.690.2328 or 1.800.690.2338 with any questions that you may have before you travel so you can avoid an interruption in service.
Phishing Scams
Phishing, pronounced "fishing," is a high tech scam that uses emails and online messages to deceive unsuspecting consumers into disclosing their credit card numbers, bank account information, social security number, passwords, or other personal and sensitive information on "look alike" websites. Phishing happens when an individual sends an email or pop-up message claiming to be from a business or organization that you may deal with, such as your Internet Service Provider (ISP), financial institution, or government agency, asking you to "update" or "verify" your information on a bogus website.
If you received an email like this claiming to be from CCU or any other financial provider, delete it. Do not click on any links in the email or call a number provided in the email. If you have any questions or concerns about an email that appears to have come from CCU, please contact us by calling 321.690.2328. More information on Phishing.
Vishing
In this variation on phishing, identity thieves are sending spam that warns victims that their credit union/bank account or PayPal accounts were supposedly compromised. However, unlike typical phishing emails, there is no website address in these phishing messages. Instead, the victim is urged to call a phone number to verify account details.
The automated voice message says: "Welcome to account verification. Please type your 16-digit card number." The goal is to get the victim to enter their credit card number. In these reported scams, no mention of the credit union, bank or PayPal is made.
Security experts tracking this scam and other instances of "vishing", short for "voice phishing", say the frauds are particularly despicable because they imitate the legitimate ways people interact with financial institutions. In fact, some vishing attacks don't begin with an e-mail. Some come as calls out of the blue, in which the caller already knows the recipient's credit card number. This increases the perception of legitimacy, the caller asks for the valuable three-digit security code on the back of the card.
Vishing appears to be prospering with the help of Voice over Internet Protocol, or VoIP, the technology that enables cheap and anonymous Internet calling, as well as the ease with which caller ID boxes can be tricked into displaying erroneous information.
Links to Helpful Government Websites:
- Secret Shopper - Fraudsters pose as companies offering mystery shopping services to dupe shopper out of money.
- Advanced Fee - Victim enticed to wire upfront fees for a fictitious promise of receiving a gift of money.
- Elderly Abuse - Seniors are tricked into sending money to help their relatives / grandkids or pay for services.
- Social Security / IRS / Government - Threaten to suspend your social security number or arrest you or take other legal action.
-
Ensure that we have your current phone numbers on record, including your mobile number. CCU uses intelligent fraud detection systems to alert you regarding possibly fraudulent transactions, but they can only be effective if we can contact you immediately when suspected fraud occurs.
-
Keep your card in a safe place.
-
DO NOT write your PIN on anything you carry with you.
-
Never loan your card to others to use.
-
Report lost or stolen cards immediately.
-
Download the SecurLOCK® app so you can control your cards from your phone or tablet.
- Government agencies do not call people out of the blue with threats or promises of money
- You cannot always trust caller ID (see 'Spoofing' above)
- You should always check with the real agency
- Government agencies will never ask you to pay with a gift card or wire transfer
- You can report government imposter scams at ftc.gov/complaint
- Never send money or gifts to a sweetheart you haven’t met in person.
- Talk to someone you trust about this new love interest. In the excitement about what feels like a new relationship, we can be blinded to things that don’t add up. Pay attention if your friends or family are concerned.
- Take it slowly. Ask questions and look for inconsistent answers. Try a reverse-image search of the profile pictures. If they’re associated with another name or with details that don’t match up, it’s a scam.
- Learn more at ftc.gov/imposters.
- Never call a number you receive from a spam email, and certainly don't enter in any private information if you make a mistake and do call. If you want to call your bank, use the normal phone number you regularly use, not the phone number you get in an e-mail.
- Never click on the link provided in an e-mail you believe is fraudulent.
- Do not open an attachment to an unsolicited e-mail unless you have verified the source.
- Do not be intimidated by an e-mail or caller who suggest dire consequences if you do not immediately provide or verify information.
- If you believe the contact is legitimate, go to the company's website by typing in the site address directly or using a page you have previously book marked, instead of a link provided in the e-mail.
- Use the FTC (Federal Trade Commission) website, OnGuard Online.
- Consumers can take interactive quizzes designed to enlighten them about identity theft, phishing, spam and online-shopping scams. Elsewhere on the site, consumers can find detailed guidance on how to monitor their credit histories, use effective passwords and recover from identity theft.
-
For Additional Assistance:
Please contact a Member Service Representative at 321.690.2328 (outside Brevard, 1.800.690.2338) or send an email to [email protected]. For your security, DO NOT send account numbers or other private information using this general email address. Private, unpublished personal information should ONLY be sent through Secure Email, which is available within the Mobile App and eBranch Online Banking.